HTTPS (Hyper Text Transfer Protocol Secure) is an extension of HTTP which is used for communication between web clients and servers. It is responsible for transmitting hypermedia documents such as HTML.
HTTPS is a secure protocol that uses SSL/TLS protocols for encrypting all the requests and responses and secures the communication between clients and servers.
In this article, I will discuss how to enable HTTPS in Apache by setting up the Secure Socket Layer (SSL) on Ubuntu Linux.
Prerequisites
To follow this guide you should have the following –
- A system running Ubuntu Linux
- Access to a user account with super user privilege
Update system package repository
Use the following command to update the apt package repository –
sudo apt updateInstalling apache
If you don’t have the apache web server installed on your system then use the following command to install it –
sudo apt install apache2 -yYou can verify the apache2 installation by checking its status –
sudo systemctl status apache2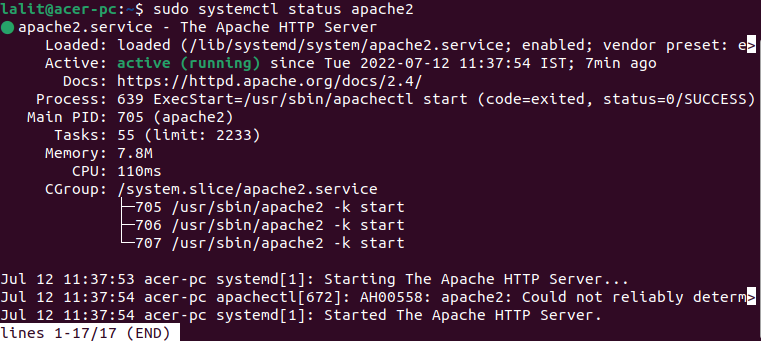
Use the following command to install OpenSSL –
sudo apt install openssl -yEnable Apache SSL module
Once the Apache and openssl packages gets installed on your system, use the following command to enable Apache SSL module –
sudo a2enmod ssl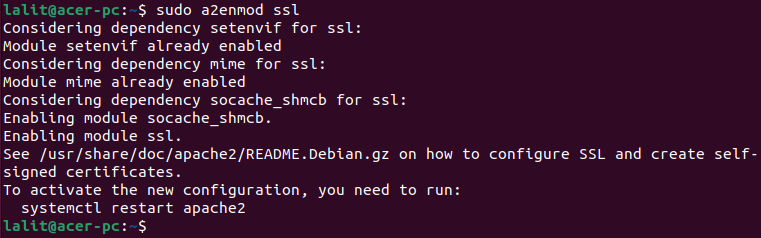
To make the changes effective you need to restart the apache2 on your system –
sudo systemctl restart apache2Create a self signed SSL certificate
A self signed SSL certificate is a certificate that is not signed or issued by a certificate authority (CA) instead it is signed with its own private key. It is good enough for trying and testing things in development phase.
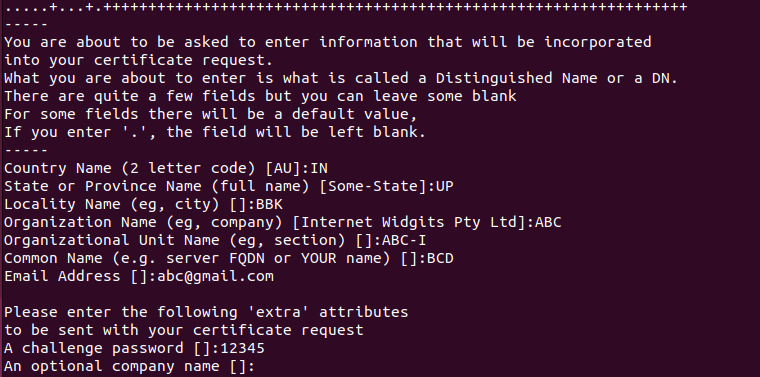
First you need to generate private key and certificate signing request for your domain. Use the following command to generate it –
sudo openssl req -nodes -newkey rsa:2048 -keyout /etc/ssl/private/private.key -out /etc/ssl/private/request.csrThis will ask you for some information for certificate like your country name, organization name, email, etc.
After request.csr is generated, now you can generate the SSL certificate by using the given command –
openssl x509 -in /etc/ssl/private/request.csr -out /etc/ssl/private/certificate.crt -req -signkey /etc/ssl/private/private.key -days 365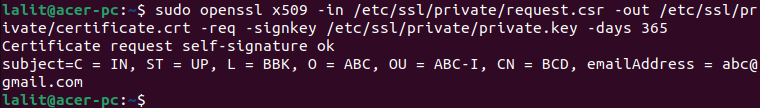
Configure Apache to use SSL
Now you need to configure your Apache webserver to use SSL so you need to edit Apache SSL configuration file.
Use the following command to open Apache SSL configuration file in a editor –
sudo nano /etc/apache2/sites-available/default-ssl.confHere edit server admin email and add domain name or IP address of the server –
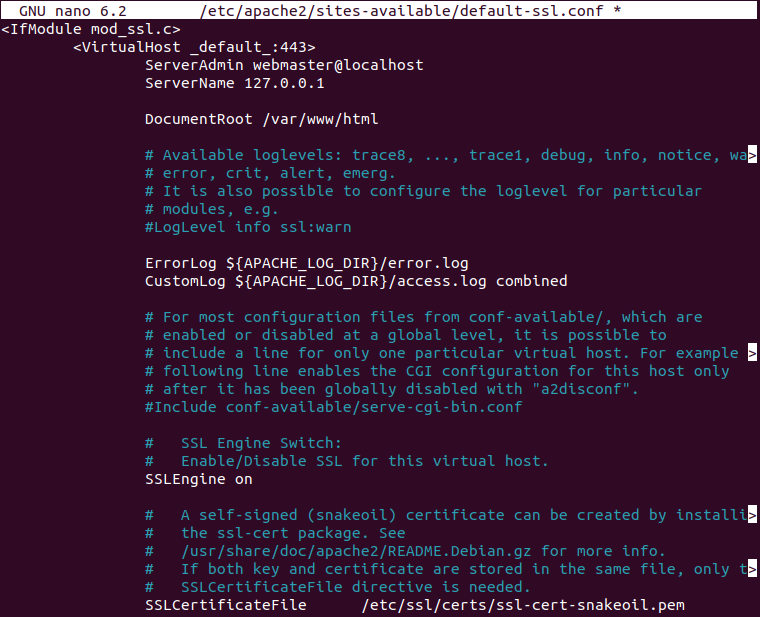
Replace the server name i.e. 127.0.0.1 with your own server IP or domain name.
Save the file by pressing Ctrl+s and then Ctrl+x to exit from the editor.
Next use the given command to enable the virtual host file –
sudo a2ensite default-ssl.confOpen the default virtual host on your apache webserver by using –
sudo nano /etc/apache2/sites-available/000-default.confHere add your domain name and add a Redirect directive, pointing all traffic to the SSL version of the site –
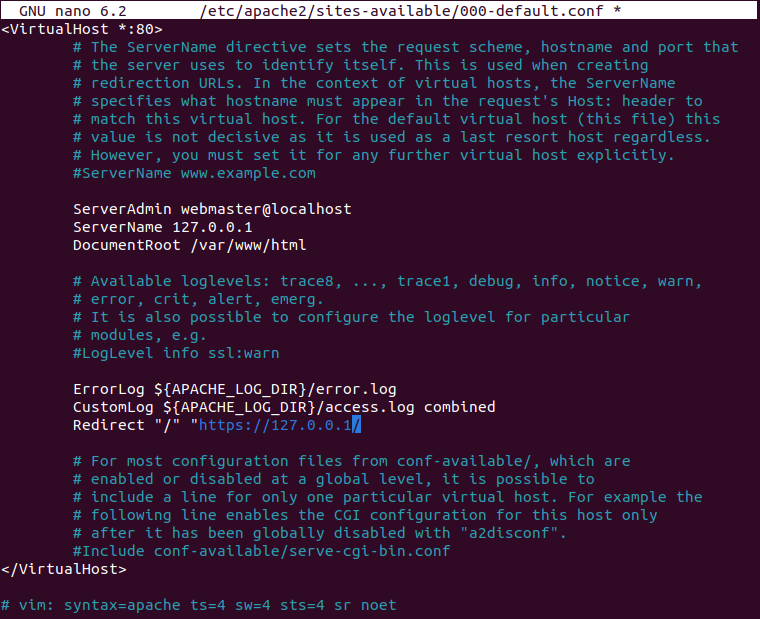
Save this file and close it.
Now enable the SSL and header module of Apache by using –
sudo a2enmod sslsudo a2enmod headersFinally, reload the Apache services to make the changes effective –
sudo systemctl reload apache2Verify your SSL server
Now to verify if you SSL server is working or not open a web browser on your system and enter the given URL –
https://server-ip-or-domainFor example –
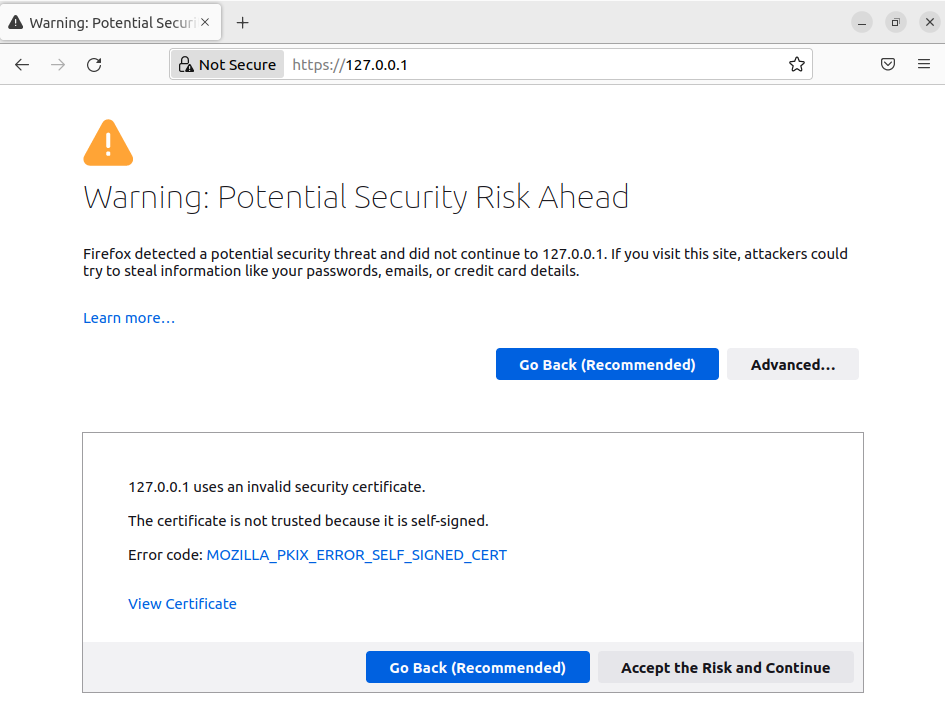
https://127.0.0.1This will display the given page initially here warning page is displayed because the certificate is self signed and not signed by a trusted CA.
Now click on the Advanced and then click Accept the Risk and Continue.
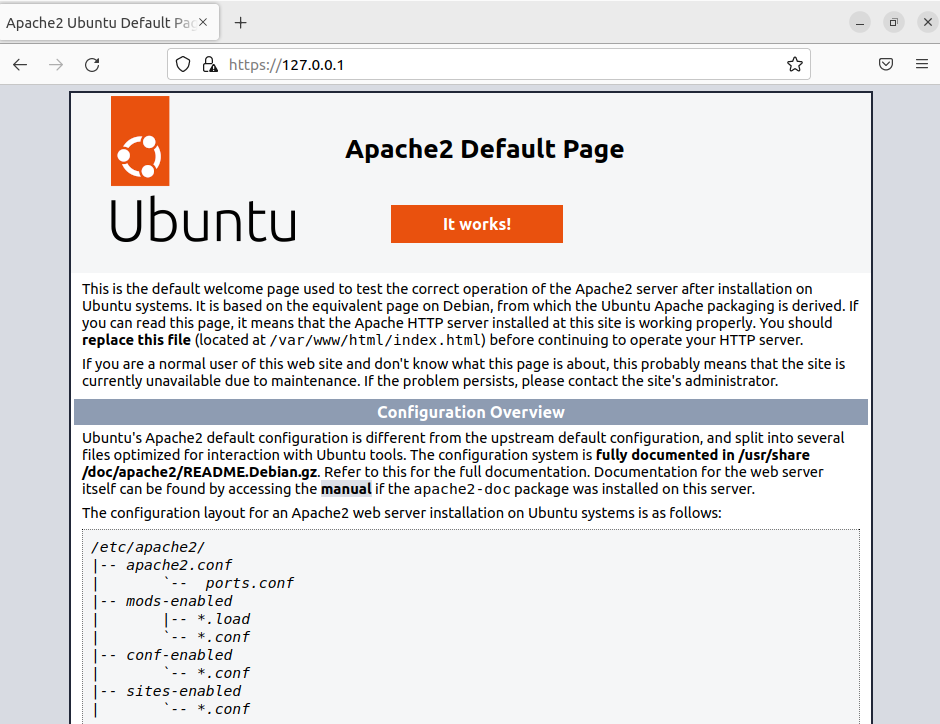
This should display the apache2 default page as you can see in the image below.
Conclusion
So you have successfully enabled the HTTPS in Apache2 web server on your Ubuntu system. Now if you have a query or feedback then write us in the comments below.
