The dig (stands for Domain Information Groper) command in Linux is used to find and display the domain information. It performs DNS lookup and fetches queries from name servers.
This command is generally used by network administrators to troubleshoot DNS problems. The dig is a more flexible and easy to use tool than other DNS lookup tools such as nslookup, host, etc.
In this article, we will discuss the usage of the dig command in a Linux system with some examples.
The syntax of the dig command
The syntax for using the dig command in a Linux terminal is given below –
dig server name type
Where,
server – It is the name or IP address of the name server to query.
name – Is the name or resource record that is to be looked up
type – The type indicates what type of query is required this can be ANY, A, MX, SIG, etc. If the type is not supplied to the command by default it will perform a lookup for A record.
DNS and types of DNS records
You can compare DNS (or domain name system) with the phonebook app on your phone in which numbers are saved with some names. Whenever you want to call someone you find the name and click on it similarly when you request some information from a website let’s say google.com, the browser first resolves and finds an IP address, and then it connects and fetches the information from the server located at that address.
A DNS server creates a record to provide important information about a domain or hostname. Some of the most common DNS record types are –
- A – Stores a hostname and it’s corresponding IPv4 address
- AAAA – Stores a hostname and it’s corresponding IPv6 address
- CNAME – Known as canonical name record can be used to alias a hostname to another one.
- MX – Mail Exchange which maps message transfer agents for the domain
- SIG – A signature record that is used in encryption protocols
There are many other records you can view their details here.
How to query A record of a domain
By default when you run the dig command without mentioning DNS type, it displays the A record of the domain name. For example – use the given command to view the A record of google.com
dig google.com
You can see the A record in the answer section in the given image-
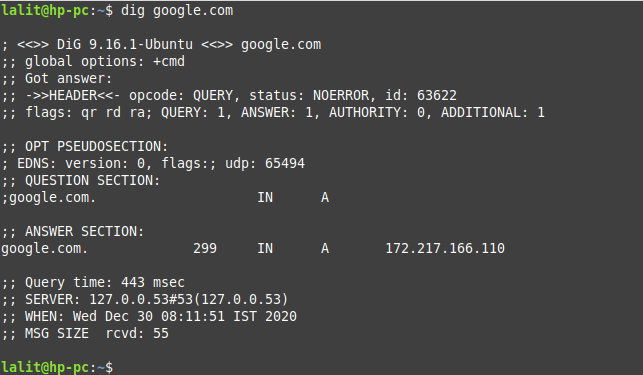
You can use various query options with the dig command to display the result in different ways. For example – using +short with command provide a terse answer by default command print output in a verbose form. You can view a detailed list of query options on its man page.
Use the given command to view details of the dig command and the query options by using –
man dig
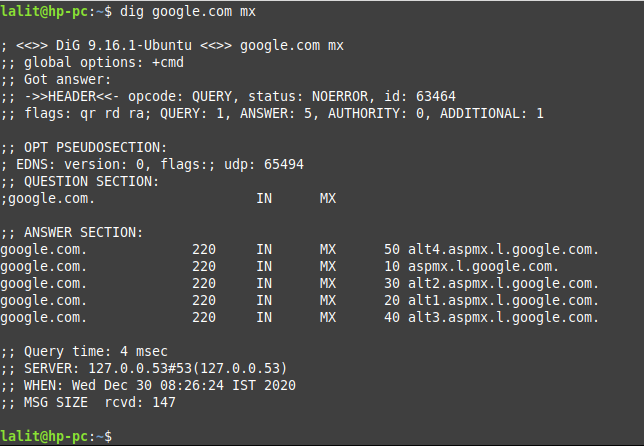
How to query MX records of a domain
Apart from A record if you want to see any other record you need to mention its type with the dig command. For example to view MX record of google.com use –
dig google.com mx
You can see the MX records in the answer section of the given image-
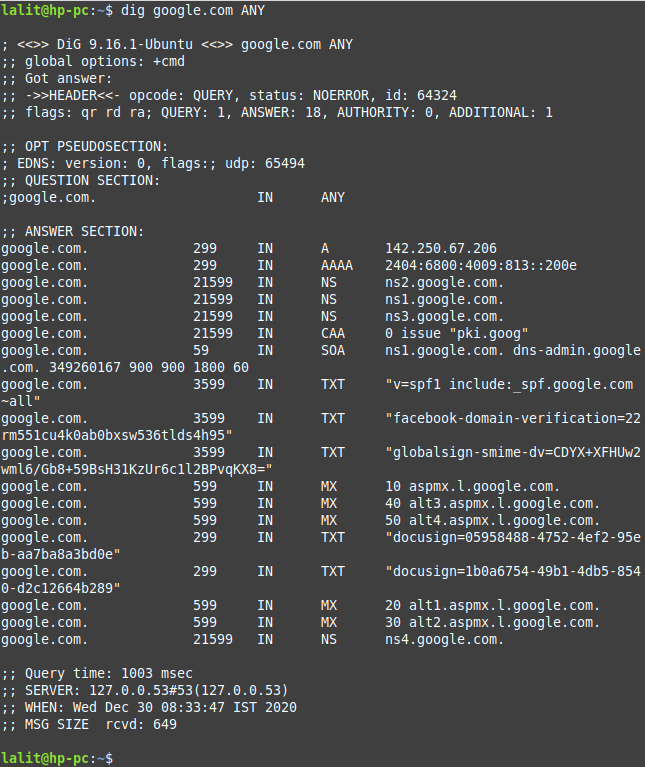
How to display all the DNS records of a domain
If you want to view all the DNS records of a domain then use the ANY type with dig command. For example to display all the DNS records of google.com use –
dig google.com ANY
Now you can see the output of this command in the following image –
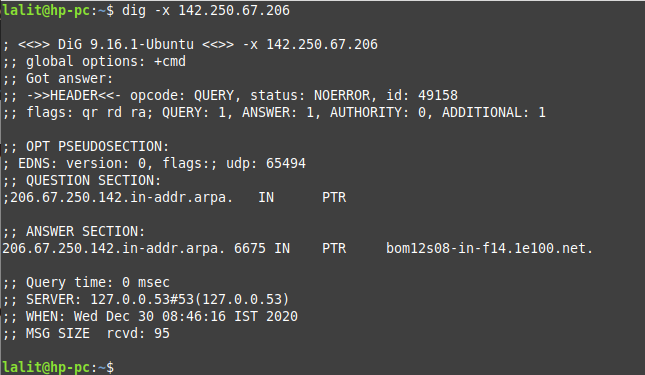
Performing reverse DNS lookup
Reverse DNS lookup means to display the host or domain name from the IP address. For example to find the host associated with 142.250.67.206 use –
dig -x 142.250.67.206
Now you can see the expected output in the given image –
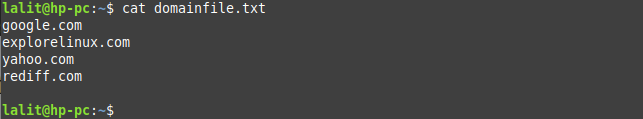
How to read lookup request from a file
The dig command also has a batch mode of operation for reading lookup requests from a file. For example, we have a file domainfile.txt that contains some domain names. you can view the content of this file by using-
cat domainfile.txt
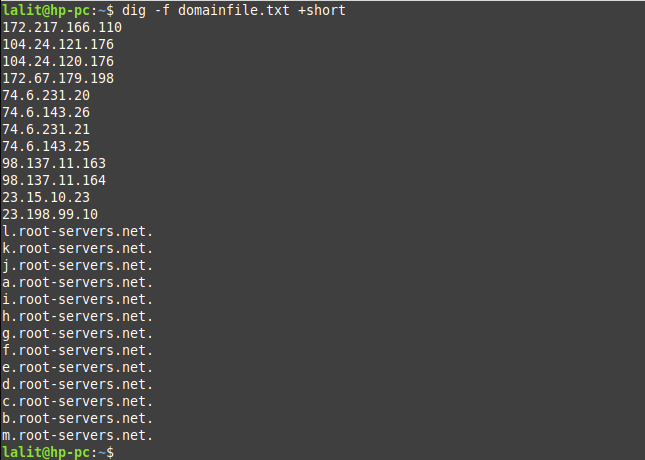
Now to perform domain-lookup on domains using this file you need to use the following command in your terminal –
dig -f domainfile.txt
Or use the query option +short to view answer in terse form –
dig -f domainfile.txt +short
You can see the output of the command in the given image.
Conclusion
Now you know how to use the dig command in Linux. If you have a query regarding this then write us in the comments below.
