Files inside a zip archive can have important data. So you may want to protect it from the unusual access. In Linux, the zip command provides a feature to set the password on zip archives.
As I already discussed to create a zip archive in Linux. In this article, we will show you how to create a password-protected zip archive or set a password on the existing zip archive in Linux.
What are zip archives?
Zip is an archive file format that supports lossless data compression. Zipping and unzipping tools are available for various platforms. Windows and macOS and many other OS are providing built-in zip support. These files generally use .zip or .ZIP file extension. A zip tool allows you to specify the compression level from 1 to 9.
How to create a password-protected zip archive?
Suppose there is a directory named sample which contains some files and directories inside it. To create a zip archive of sample directory, use the following command in the terminal –
zip -r sample.zip sample
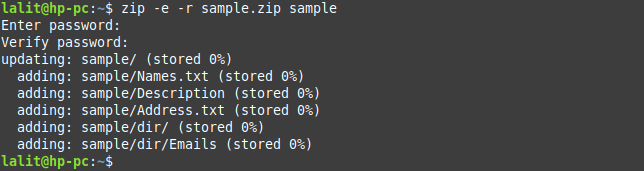
This command will create a zip file without any password. To create a password-protected zip archive, use the following command in the terminal-
zip -e -r sample.zip sample
How to set a password on an existing zip file?
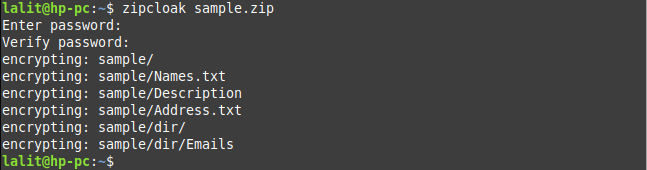
Suppose there is a zip file named sample.zip that is not password protected. If you want to set a password on it then you could use the following command in your terminal –
zipcloak sample.zip
Once this command gets executed it will prompt you to enter the password for sample.zip file.
Extracting a password-protected zip file
It requires entering the password if you want to extract a password protected zip file. Use the following command and enter the password if prompted –
unzip sample.zip
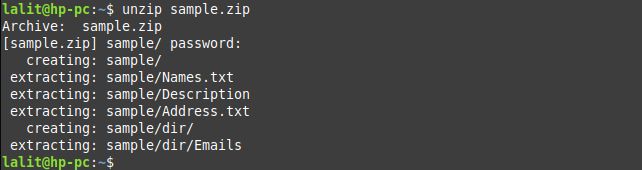
Once you enter your password and press return key first it will create a directory with the name sample and then extract all the files and directories into this directory.
Conclusion
There are a lot of options available that you can use with the zip command. You can see the manual page of the zip for more details. Now if you want to say something on this topic then write your thoughts in the comments below.
