One-time Password In Everything(OPIE) is a security feature in FreeBSD that prevent a system from replay attack. In a replay attack, an attacker discovers the password of a user and use it to access the system. Since a password used only once in OPIE so discovered password is of little use to an attacker.
In this article, you will learn to generate and use the one-time password using OPIE to login to a remote FreeBSD system.
Adding a new user
First, you should try this feature by creating a separate user account so that you do not end up locking your remote server. You can use the following command to add a user on FreeBSD –
# adduser
Once this command gets executed it will ask details such as username, password, home directory, etc enter it. Finally, confirm that the information provided is correct. Press y and then enter.
Here I added a user named lalit in my system.
Login into the newly created user account
Now from the current terminal enter the following command to login into newly created user account –
ssh user_name@ip_of_server
For example –
ssh lalit@localhost
This will ask the current user password, enter it to get proceeded. Login using ssh is important because the OPIE setup requires a secure terminal.
Enable OPIE for new user
Use the following command to enable the OPIE for the new user. Be careful, Once this gets enabled you will not be able to access the system with the normal password.
opiepasswd -c
Option -c tells the command that this system is trusted.
When this command executes you will be asked to enter the secret passphrase, enter your passphrase at least ten characters long e.g my secret pass phrase. Enter the same passphrase in the next line also.
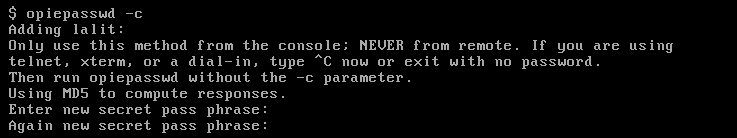
If passphrase matches you will get a new OPIE seed and a randomized passphrase.
![]()
Here 499 is the iteration count and sr7612 is the OPIE seed. Now open the new terminal on your local machine and run the following command –
ssh lalit@localhost
You will receive the following output. It will ask you to enter the one-time password instead of a normal user password.
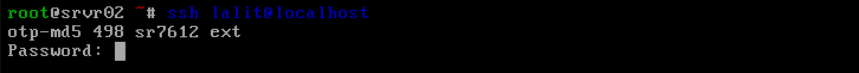
You have not created the one-time password yet so let’s create it.
Create the one-time password
First, close this terminal and back to the previous one where you are login with your username. And then run the following command –
opieinfo
![]()
You need to remember sequence number 498 and OPIE seed value sr7612 to generate the one-time password.
Now use the following command to generate the OTP –
opiekey 498 sr7612
or use –
opiekey `opieinfo`This will ask you to enter your secret passphrase, enter it –
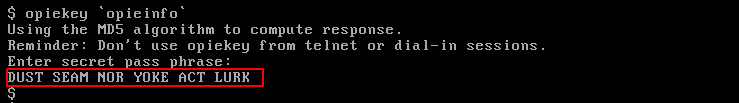
The last line which is highlighted in red containing six words is the OTP.
[alert color=”yellow”] Note: Always generate your one time password from a secure location[/alert]Now open a new terminal and run –
ssh lalit@localhost
and then if it asks to enter a password, enter the newly generated one-time password. You will be successfully login into it.
Now open a new terminal and try to login into the same account by using –
ssh lalit@localhost
you will now see that sequence number is decremented by one.
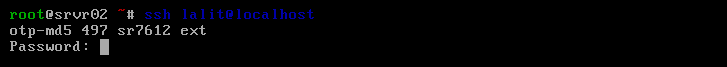
To log in to this, you need to generate new OTP using sequence number 497 and seed value sr7612.
opiekey 497 sr7612
How to create multiple OTPs
It is possible that you do not have access to a trusted computer for a long period of time. So you can create multiple OTPs and can use them later to log in to your server multiple times. You can use the following command to create multiple OTPs –
opiekey -n 5 `opieinfo`This command will generate five OTPs with the consecutive sequence number that you can use later to log in to your server.
To know more about OPIE you could visit FreeBSD One-time Passwords.
Conclusion
The OPIE is useful to those who travel to different places and access the server from public computers and networks. Now if you have anything to ask then you can write to us in the comments below.
